On Demand Build Infrastructure on OCI Ampere A1 with Terraform

Often, when working on complex software stacks, you need the ability to quickly build from source and package your project to swiftly deploy and test. Using cloud APIs to dynamically create that infrastructure and automatically build your software and package it for deployment can give you tremendous flexibility and allow you to iterate quickly within your dev/test cycle.
In this tutorial, we will show you an example of how easily this can be done on Ampere® Altra® Multi Core Server Processors and spotlight the key benefits of the world’s first cloud native processors (CNPs).
OpenStack Kolla is a sub project of the larger OpenStack project. It provides a way to build all the OpenStack services as containers. As those who have used OpenStack know, building OpenStack from source can be necessary at times to be able to take advantage of a patch fix prior to an official release. In this post, we will build upon previous work to quickly build OpenStack Kolla dynamically using Ampere Altra processors within Oracle Cloud Infrastructure (OCI) on Ampere A1 shapes.
Requirements
To automate, we will use the DevOps tool Terraform to fork and extend that module to create an on-demand build infrastructure for OpenStack Kolla containers.
Before you start:
- Install Terraform on your system
- Sign up to Oracle OCI “Always Free” Account and find your credentials for API use
Forking the oci-ampere-a1 terraform module
The oci-ampere-a1 terraform module code supplies the minimal amount of information to quickly have working Ampere A1 shapes on OCI “Always Free”. It has been forked and functionality added to allow to quickly build OpenStack Kolla with a series of parameters that can be passed in. To keep things simple from an OCI perspective, the root compartment will be used (compartment id and tenancy id are the same) when launching any shapes. Some of the tasks performed by this terraform code are:
- Operating system image id discovery in the user region.
- Dynamically creating SSH keys to use when logging into the shape.
- Dynamically getting region, availability zone and image id.
- Creating necessary core networking configurations for the tenancy
- Rendering dynamic values into metadata, scripts to pass into the Ampere A1 shape.
- Rendering dynamic values into files to write to the management station running terraform.
- Launch on Ampere A1 shapes with metadata and SSH keys.
- After metadata run is complete pass in rendered scripts then execute scripts on remote host.
- Output IP information to connect to the shape.
Cloning the repository
To start out, we must clone the terraform code repository. You will need to have git installed. Open your terminal and type the following commands to clone the repository:
git clone https://github.com/amperecomputing/terraform-oci-ampere-openstack-kolla-image-builder cd terraform-oci-ampere-openstack-kolla-image-builder
Configuring Terraform with terraform.tfvars
Next, we will need to configure authentication credentials for Terraform to use. To do this we will quickly configure Terraform using a terraform.tfvars file within the project directory. Please note that Compartment OCID are the same as Tenancy OCID for Root Compartment. The following is an example of what terraform.tfvars should look like:
tenancy_ocid = "ocid1.tenancy.oc1..aaaaaaaabcdefghijklmnopqrstuvwxyz1234567890abcdefghijklmnopq" user_ocid = "ocid1.user.oc1..aaaaaaaabcdefghijklmnopqrstuvwxyz0987654321zyxwvustqrponmlkj" fingerprint = "a1:01:b2:02:c3:03:e4:04:10:11:12:13:14:15:16:17" private_key_path = "/home/bwayne/.oci/oracleidentitycloudservice_bwayne-08-09-14-59.pem"
For more information regarding how to get your OCI credentials please refer to the following reading material:
Running Terraform
Executing terraform is broken into three commands. First you must initialize the terraform project with the modules and necessary plugins to support proper execution. The following command will do that:
terraform init
Below is output from a ‘terraform init’ execution within the project directory.
After ‘terraform init’ is executed it is necessary to run ‘plan’ to see the tasks, steps, and objects. that will be created by interacting with the cloud APIs. Executing the following from a command line will do so
terraform plan
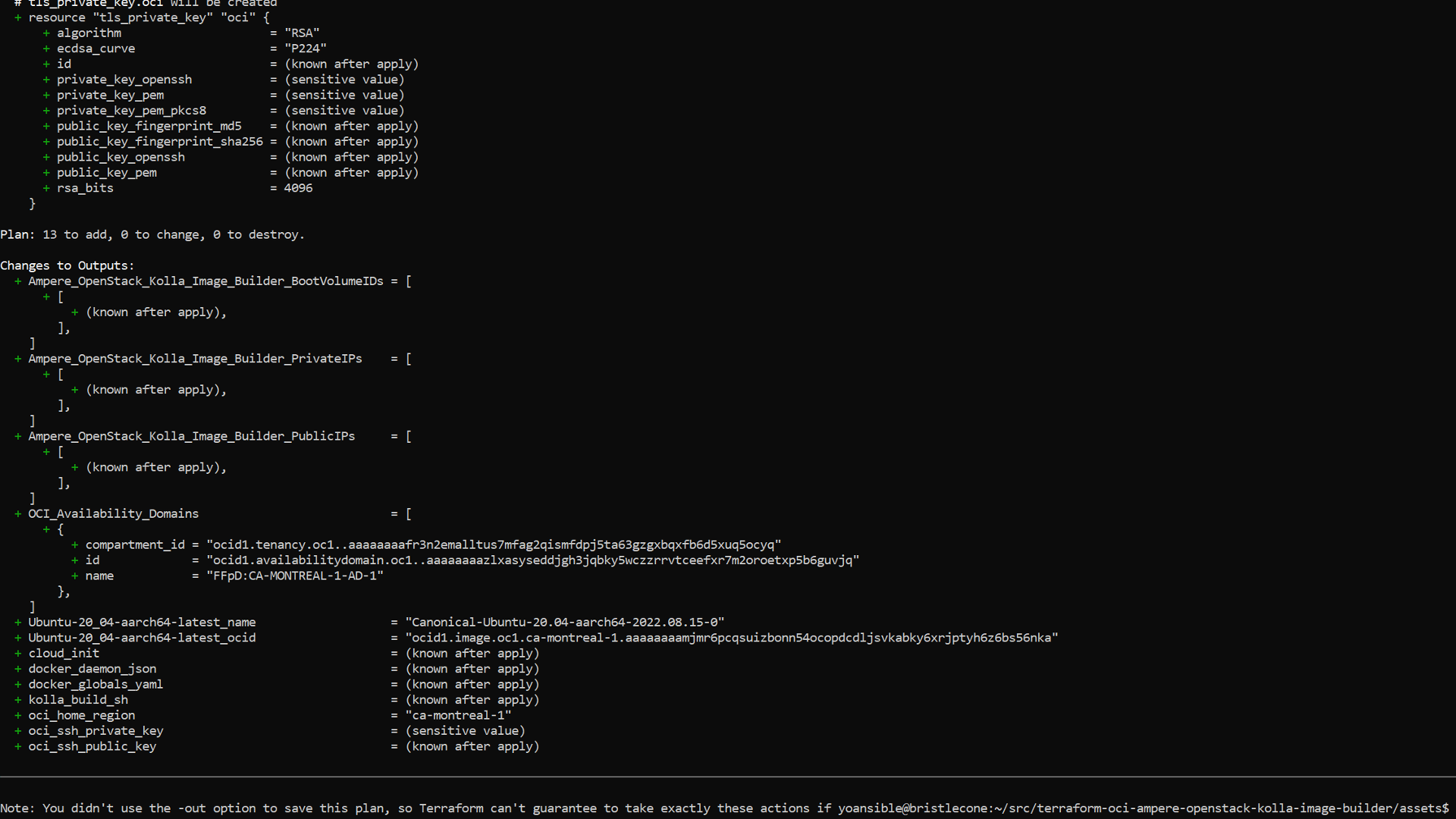
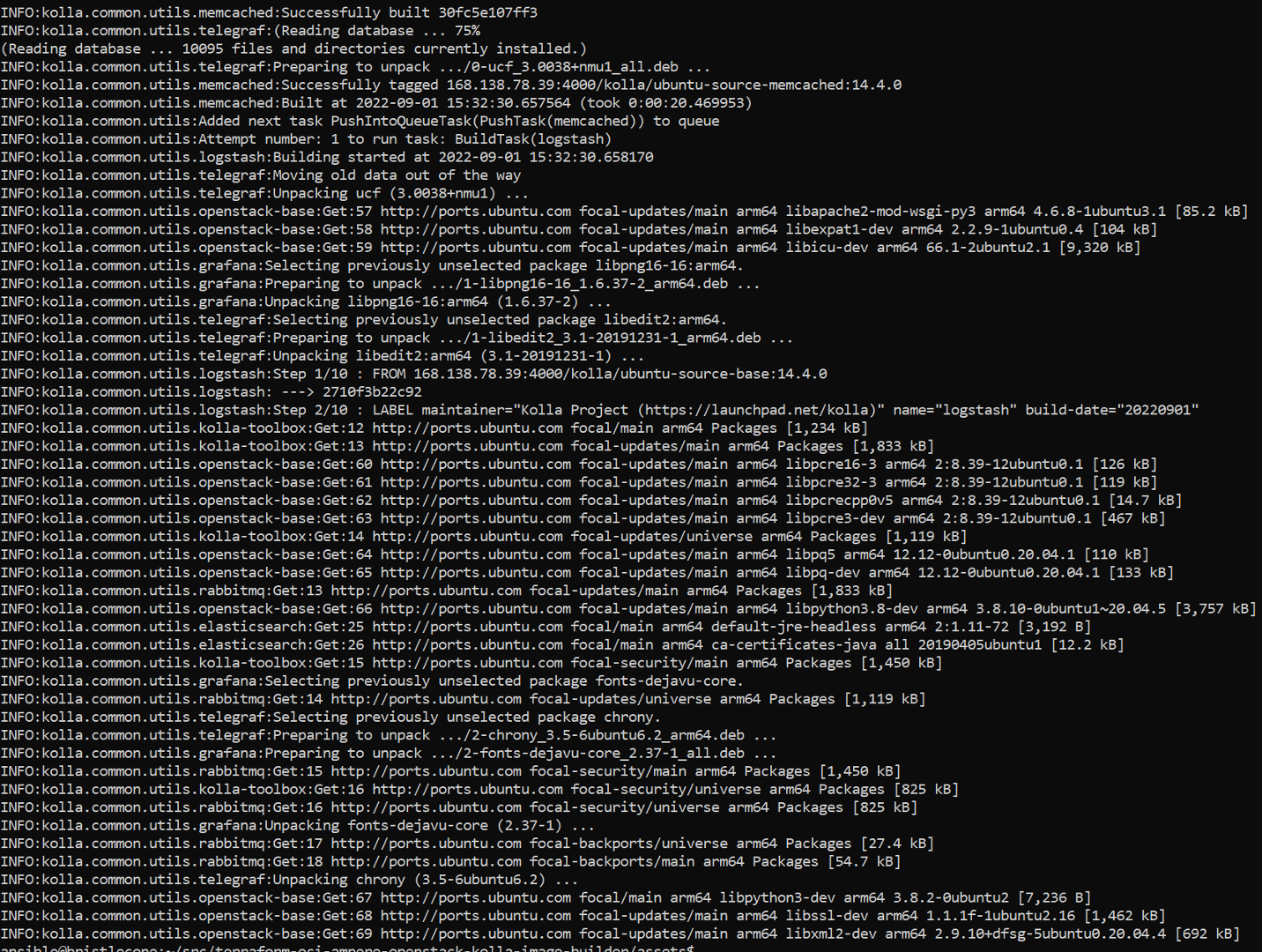
The output from a ‘terraform plan’ execution in the project directory will look like the following:
Finally, you will execute the ‘apply’ phase of the terraform execution sequence. This will create all the objects, execute all the tasks, and display any output that is defined. Executing the following command from the project directory will automatically execute without requiring any additional interaction:
terraform apply -auto-approve
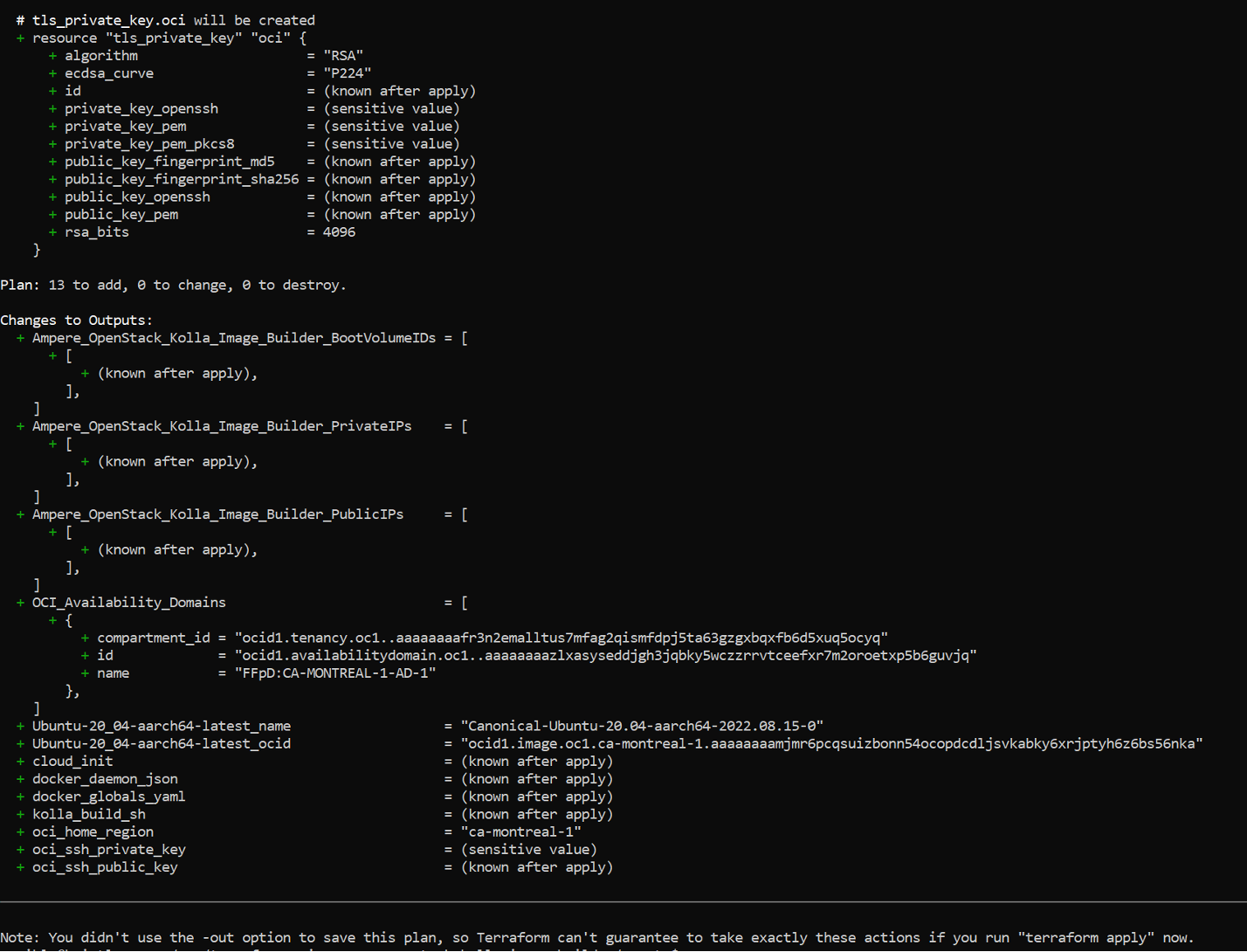
The following is an example of output from a ‘apply’ run of terraform from within the project directory:
Logging in
Next, you’ll need to login with the dynamically generated SSH key that will be sitting in your project directory. To log in take the IP address from the output above and run the following SSH command:
ssh -i ./oci-is_rsa opc@155.248.224.67
You should be automatically logged in after running the command.
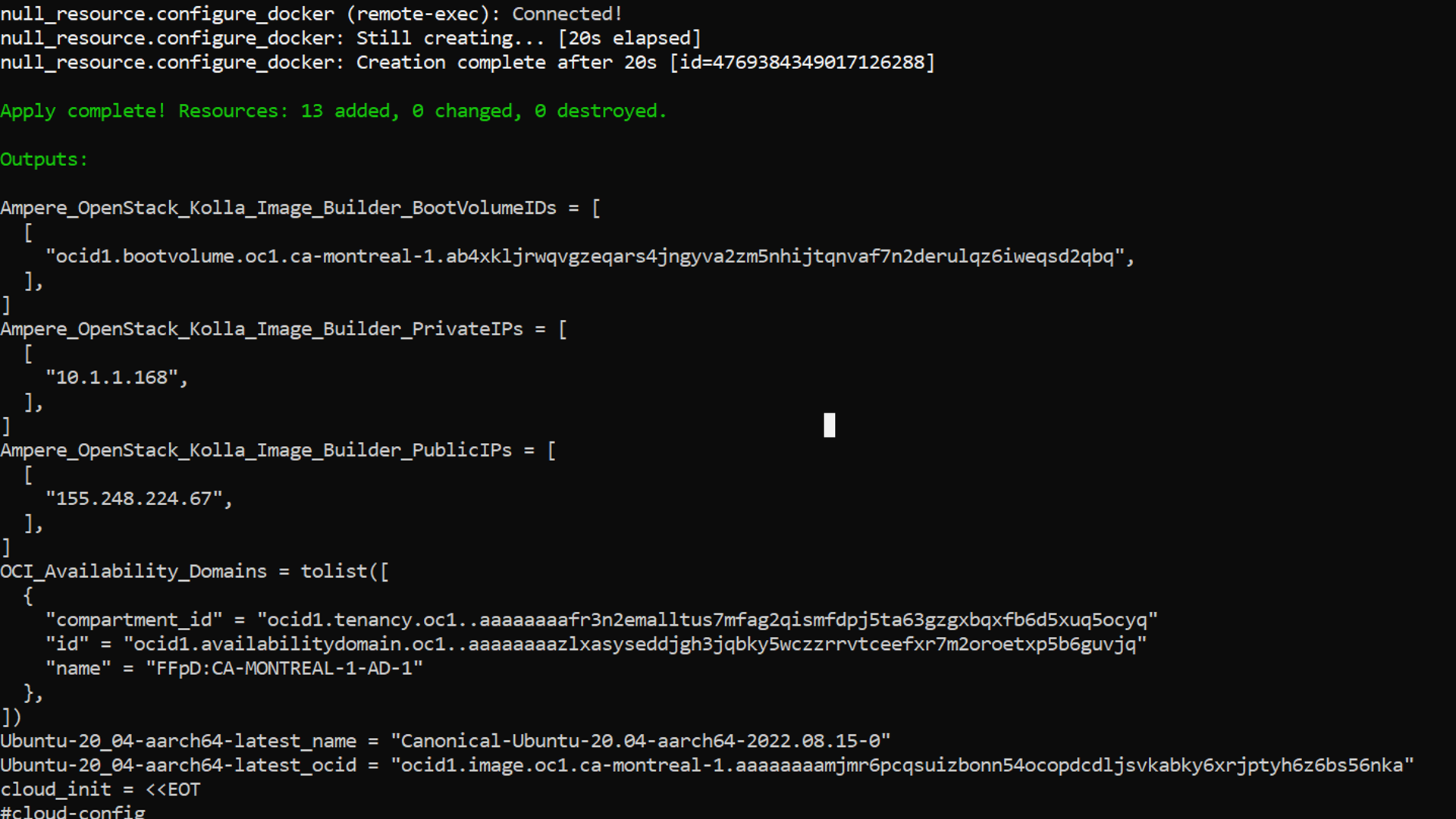
Verify that the metadata is executing by checking ‘/var/log/cloud-init.log’ and ‘/var/log/cloud-init-outoput.log’. The following is output from sshing into an shape and then running ‘tail -f /opt/kolla-build/build_kolla_containers_.log’ to verify the containers began building properly:
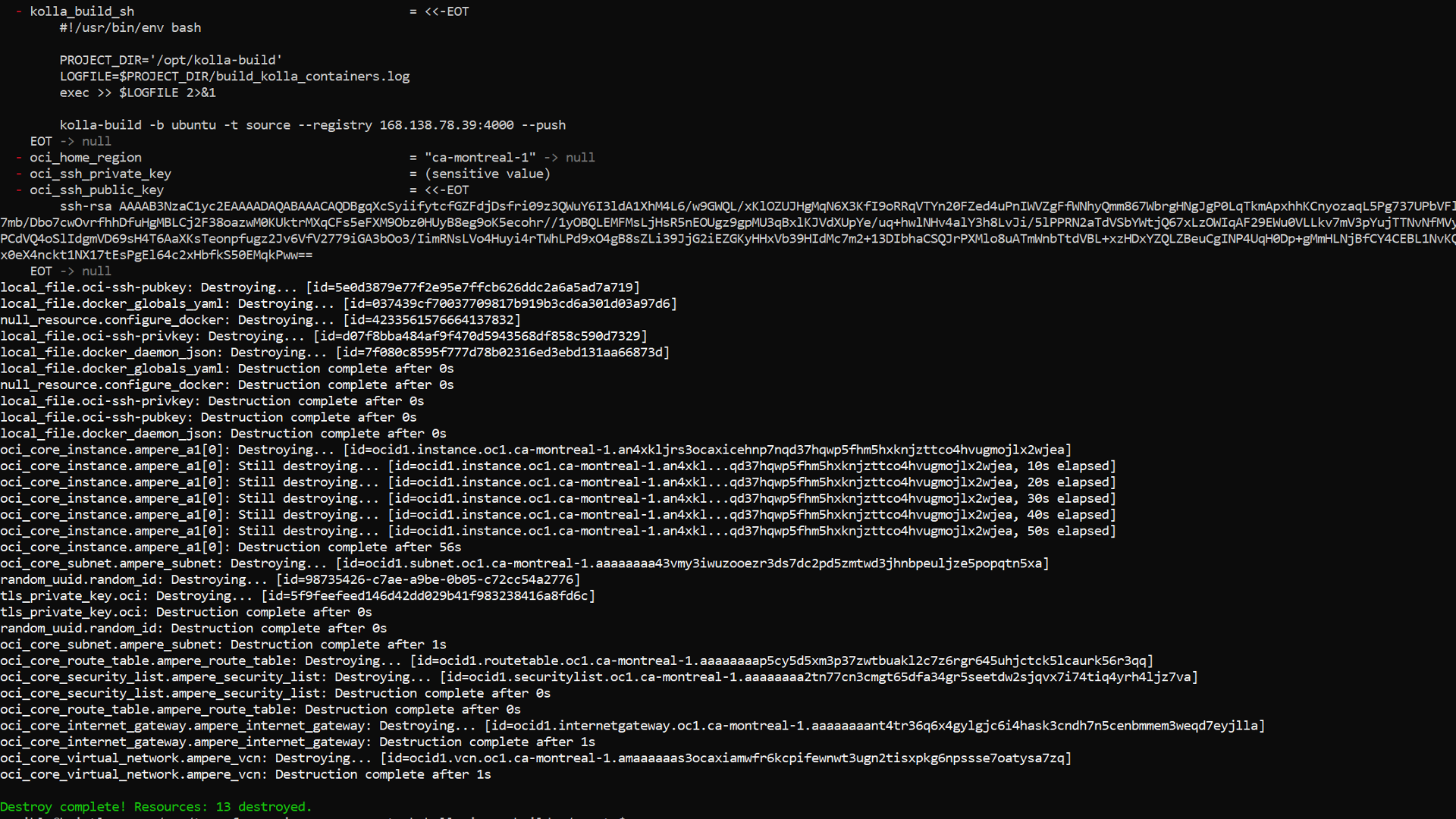
Destroying when done
Once container building is complete you will have successfully used OpenStack Kolla to build usable containers from source that are available to retrieve from the container registry running on your Ampere A1 host. When you are finished with these or need to build new ones you can quickly destroy the infrastructure. To do so you will need to execute the ‘destroy’ command to remove all created objects in a ‘leave no trace’ manner. Execute the following from a command to remove all created objects when finished:
terraform destroy -auto-approve
The following is an example of output from ‘terraform destroy’ when used on this project.
Modifying the variables for the OpenStack Kolla version to build and then performing the same workflow will give you fresh containers containing the OpenStack services using the newly supplied version. At this point you should know how to be able to use OCI Ampere A1 shapes for on demand build infrastructure.
